Technologies / Solutions
- Home
- Technologies / Solutions
Technologies \ Solutions
Cyber Security
Cyber security is the application of technologies, processes and controls to protect systems, networks, programs, devices and data from cyber attacks. It aims to reduce the risk of cyber attacks and protect against the unauthorised exploitation of systems, networks and technologies.

Advanced Threat Protection
Advanced threat protection (ATP) is defined as an array of security solutions that defend against complex malware and cyber attacks that target sensitive data. ATP technology can help an organization adapt to the ever-changing strategies of cyber criminals and better anticipate and prevent costly security breaches.

Data Security
Data security refers to the process of protecting data from unauthorized access and data corruption throughout its lifecycle. Data security includes data encryption, hashing, tokenization, and key management practices that protect data across all applications and platforms.

Application Security
Application security describes security measures at the application level that aim to prevent data or code within the app from being stolen or hijacked. Application security may include hardware, software, and procedures that identify or minimize security vulnerabilities.

Endpoint Security / XDR
Extended Detection and Response (XDR) is a SaaS-based, vendor-specific, security threat detection and incident response tool that natively integrates multiple security products into a cohesive security operations system that unifies all licensed components.
User Security
User Security consists of the platforms which protect your organisation’s users, endpoints and their online activity to more efficiently correlate threats. As users are increasingly logging in to networks via their personal devices, securing these is just as important as securing company owned devices.

Cloud and Infrastructure Security
The term cloud computing infrastructure security refers to the entire infrastructure, which involves a comprehensive set of policies, applications, and technologies. It also includes controls that are used to protect virtualized IP, services, applications, and data.

Web Application Security
Web application security refers to a variety of processes, technologies, or methods for protecting web servers, web applications, and web services such as APIs from attack by Internet-based threats.
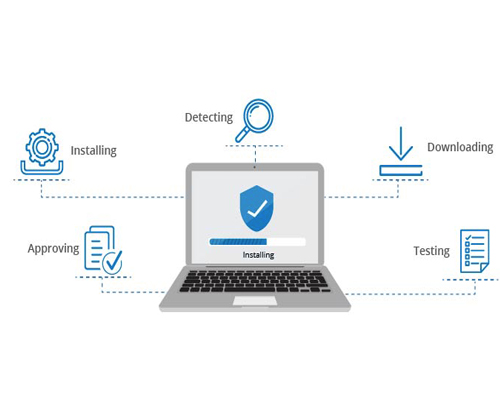
Vulnerability and Patch Management
Vulnerability management is a continuous process of identifying, prioritizing, remediating, and reporting on security vulnerabilities in systems and the software that runs on them.
Patch management is a critical component of vulnerability management, but it’s just one piece of the puzzle.